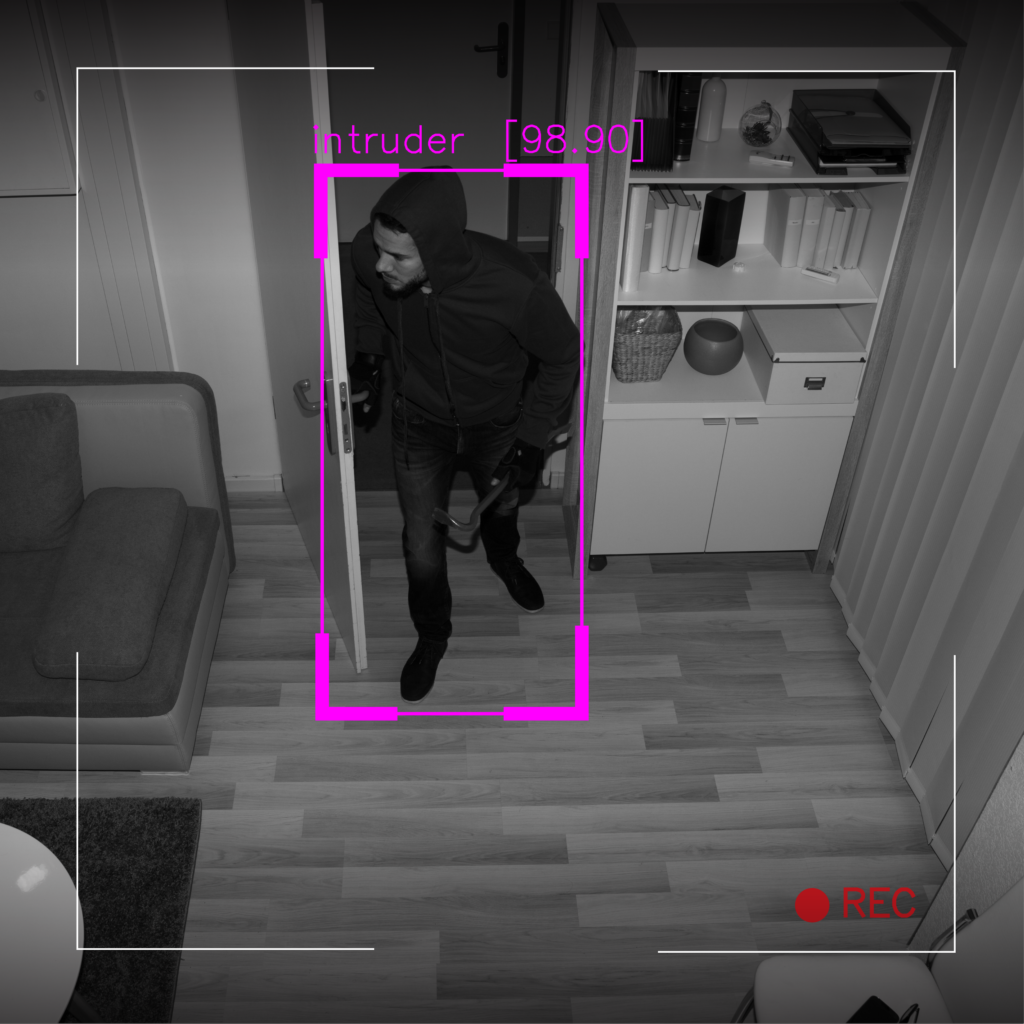
As artificial intelligence continues to advance, there is growing concern over the ethical implications of AI-enabled video surveillance, particularly concerning privacy and bias. A 2019 American Civil Liberties Union report warns that such technology may compromise our civil liberties in dangerous ways. However, ethical considerations do not necessarily have to come at the expense of safety.
 Blogs
Blogs 












